Setting Mikrotik as IPSec Concentrator
This tutorial is on setting Mikrotik as IPSec concentrator. Road-Warriors will be able to establish secure IPSec connection using the ShrewSoft VPN client.
Setting Mikrotik IPSec parametars
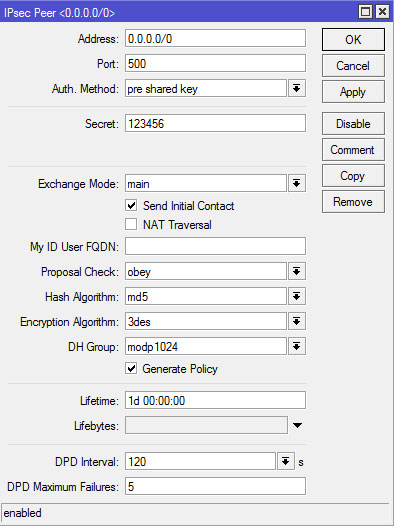
Since Road-Warriors will connect from different locations we need to set peer with address 0.0.0.0/0 and automatically generate polixy
/ip ipsec peer add address=0.0.0.0/0 auth-method=pre-shared-key exchange-mode=main\ secret=123456 hash-algorithm=md5 enc-algorithm=3des generate-policy=yes
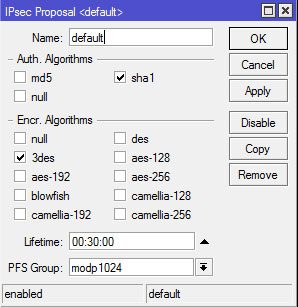
Make sure that the default proposal has Authentication algorithm sha1 and Encryption algorithm 3des
Setting ShrewSoft VPN Client
Put the Mikrotik router Public IP address in Remote Host and change the Local Host to Use existing adapter and current address

Disable NAT Traversal and IKE Fragmentation if you are not using NAT Traversal

If you need WINS and Local DNS put it manually, otherwise disable this parameters

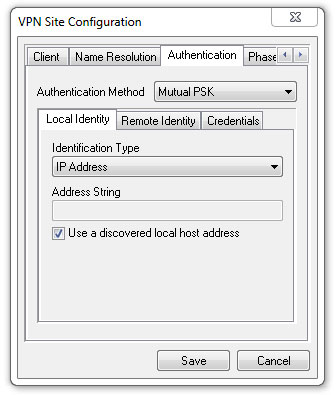
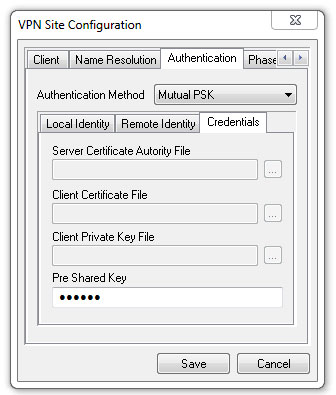
Under Authentication set Authentication Method as Mutual PSK, Local Identity as IP Address and put the secret in Credential -> Pre Shared Key
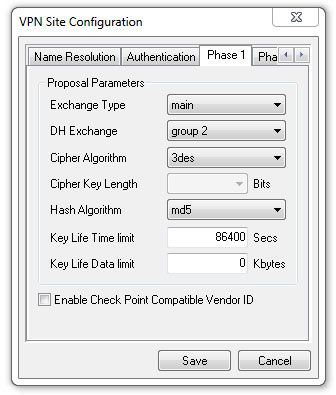
Set the Phase1 Parameters to match Mikrotik Peer configuration: main, group2, 3des, md5, 86400
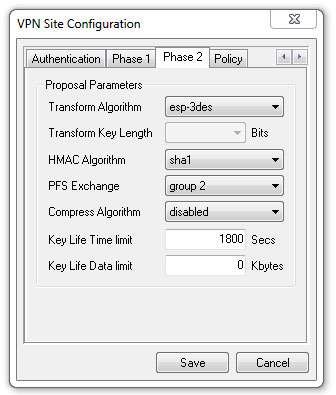
Set the Phase2 Parameters to match Mikrotik default proposal: esp-3des, sha1, group2, and change the Key Life Time limit to 1800 because in Mikrotik default proposal Lifetime is 00:30:00
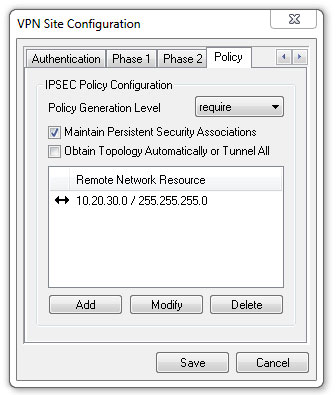
Finally we need to add the local network (10.20.30.0/24) that we want to route trough the IPSec VPN connection.
That’s it! You have your 50$ IPSec VPN Concentrator without the need to buy additional licences or expensive routers.
Mikrotik: http://www.mikrotik.com
Mikrotik Wiki: http://wiki.mikrotik.com
Shrew Soft: http://www.shrew.net








Hello Nikola ,
First of all thanks for the instructions which are very useful and helpful .
My question if you ever try the “IPSEC L2TP Microsoft VPN” feature using the Mikrotik router, i tried several times and haven’t succeeded as opposed to the PPTP Microsoft feature thet works fine .
because of the securuty issue i still would prefer using the IPSEC VPN rather than PPTP.
Thanks
Koby, I have done and still use the Mikrotik L2tp VPN to connect to my office network from home and it works just fine. The good thing is that it can be set up to use IPSEC for encryption. See here: https://www.timigate.com/2017/02/very-easy-way-to-configure-mikrotik.html?m=1